We are a manufacturer of ONVIF-complaint video streaming devices.
We have support for a number of VMS implementations, however with XProtect we experience an issue we were not able to cope with internally.
It looks like it has something to do with how XProtect caches information about the provisioned devices.
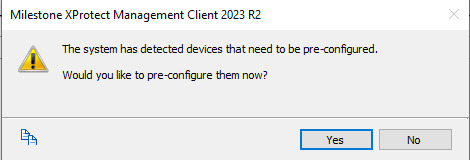
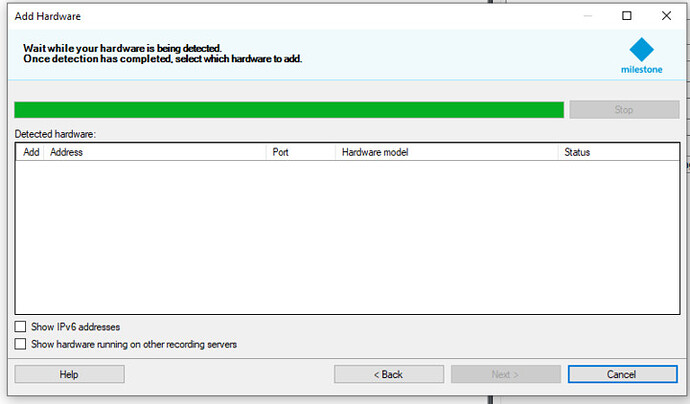
In general the problem is that with certain version of our software in a specific state we aren’t able to use ONVIF (auto) discovery.
As it seems the Xprotect Management Client (XMC) does not list our device despite it being probed and replying correctly with a WSDD response.
There are several observations we have already made up until now, but looks like we are unable to proceed anymore without additional support from your side.
We have observed that:
1. We still are able to add devices manually (by their IPs) in all cases
2. The other VMSs we have support for are able to discover the devices correctly
3. The sequence of ONVIF APIs called in the repro and non-repro case are different, however the payloads and our device’s responses are the same for the same API calls.
### repro
00. WSDD_Probe|
01. WSDD_ProbeMatches|
1. Device::GetServices|
2. Device::GetNetworkInterfaces|
3. Device::GetNetworkInterfaces|
4. Media::GetVideoSources|
5. Device::GetNetworkInterfaces|
6. Media::GetAudioSources|
7. Device::GetNetworkInterfaces|
8. Media::GetAudioOutputConfigurations|
9. Device::GetServices|
10. Device::GetServices|
11. Device::GetNetworkInterfaces|
12. Device::GetNetworkInterfaces|
13. Media::GetVideoSources|
14. Device::GetNetworkInterfaces|
15. Media::GetAudioSources|
16. Device::GetNetworkInterfaces|
17. Media::GetAudioOutputConfigurations|
18. Device::GetNetworkInterfaces|
19. Device::GetDeviceInformation|
### non-repro
00. WSDD_Probe|
01. WSDD_ProbeMatches|
1. Device::GetServices|
2. Device::GetNetworkInterfaces|
3. Device::GetNetworkInterfaces|
4. Media::GetVideoSources|
5. Device::GetNetworkInterfaces|
6. Media::GetAudioSources|
7. Device::GetNetworkInterfaces|
8. Media::GetAudioOutputConfigurations|
9. Device::GetServices|
10. Device::GetUsers| (failed due to insufficient permissions)
11. Device::GetNetworkInterfaces|
12. Device::GetDeviceInformation|
The sequences differ from call 10. on, however requests and replies for 9. are the same for both cases.
4. The above is all observed on XProtect 2023 r2, however it was present in older versions (presumably 2022 r3)
5. We’ve also noticed a very curious behavior: when this reproduces and wrong device password is entered the device would appear in the auto-discovery box in XMC.
Of course, at this stage, the device would not be added, but it is show on the list.
Entering correct password goes back to the same state where it is not displayed and can be added only by IP.
Questions:
1. Essentially, there is no difference in state, we were able to identify, between a device which reproduces this and a one that doesn’t.
We suspect there must be some, however we are unaware what exactly. It might be something relevant to XMC that does not seem obvious to us.
Please let us know if there’s any reason why XMC could behave differently.
2. What could be the reason for calling `Device::GetUsers` API ?
2.1. Could failing to get a response to `Device::GetUsers` be a reason why auto discovery fails ?
Please let us know if there are any additional information that we could provide and are relevant for the cause.